Multi-Tenant Underwriting Platforms: Isolating Health Data Across Carriers
An insurance-technology analysis of how multi-tenant underwriting platforms isolate health data across carriers while balancing speed, auditability, and shared infrastructure.
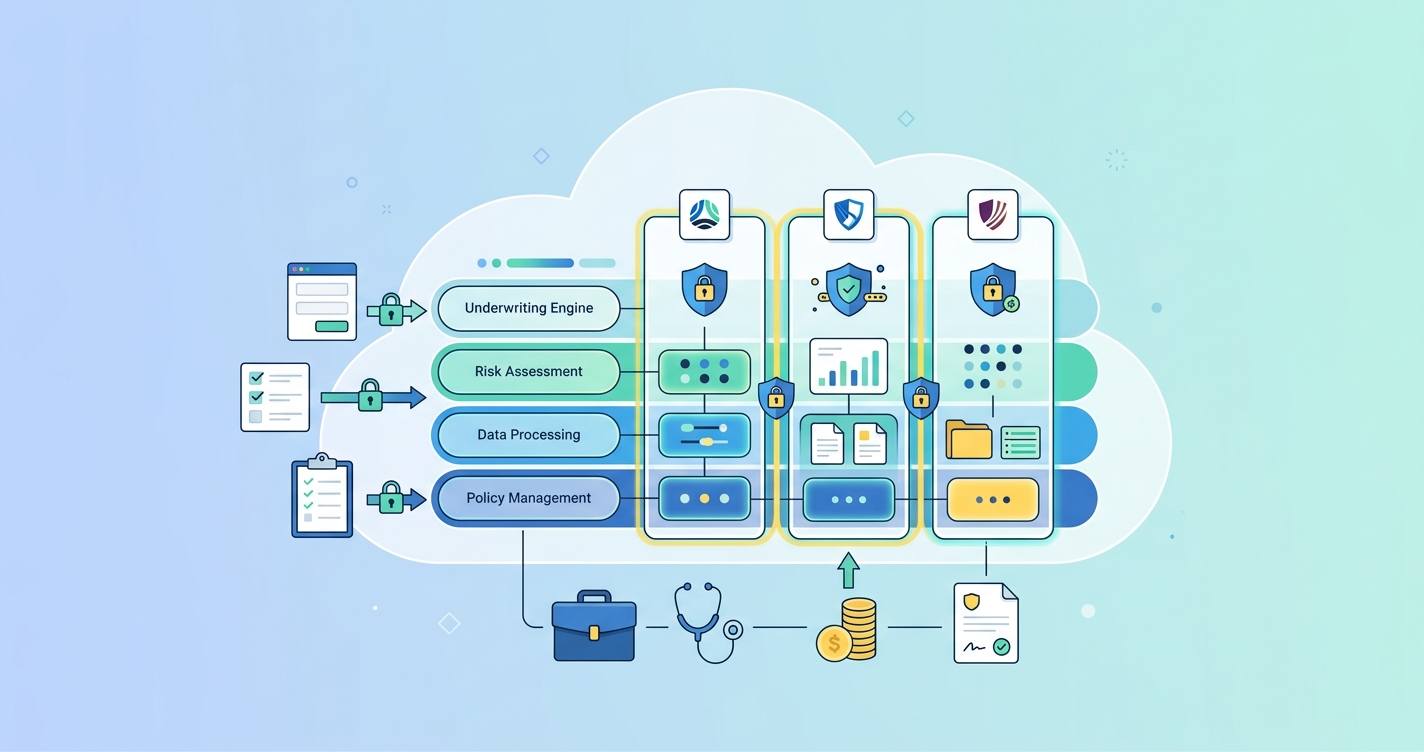
A multi-tenant underwriting platform health data isolation strategy has moved from a backend architecture concern to a board-level issue for carrier platforms, MGA stacks, and underwriting vendors. As more insurance teams ingest richer health-screening data through APIs, the platform question is no longer whether several carriers can share the same infrastructure. It is whether they can do so without mixing policies, permissions, audit trails, and protected health data in ways that create operational or regulatory risk.
“Organizations retain ultimate responsibility and accountability for the security and privacy of data and applications implemented and deployed in public cloud computing environments.” — Wayne Jansen and Timothy Grance, NIST SP 800-144
Multi-tenant underwriting platform health data isolation: what actually matters
Multi-tenancy is attractive because it lowers operating cost, speeds product rollout, and lets platform teams reuse workflows across carriers. Cor-Paul Bezemer and Andy Zaidman described that economic logic in their 2010 work on multi-tenant SaaS, arguing that shared application and database layers can improve hardware utilization and simplify deployment. But they also warned that the wrong architectural choices can turn multi-tenancy into a maintenance problem instead of a scale advantage.
That warning lands differently in underwriting than it does in generic SaaS. Insurance platforms are not just storing preferences or invoices. They may be handling applicant identity data, questionnaire responses, third-party records, decision outputs, and health observations used in risk scoring. When a single platform serves multiple carriers, the isolation model has to cover more than storage. It has to separate:
- carrier-specific applicant records
- carrier-specific access controls and service accounts
- model versions, rules, and thresholds
- document retention schedules and audit logs
- reporting, analytics, and downstream event streams
In practice, that means tenant isolation has to be enforced at several layers at once.
| Isolation layer | What must be separated | Common control pattern | Main platform risk if weak | |---|---|---|---| | Identity and access | Users, API clients, service roles | Tenant-scoped IAM, least privilege, separate signing keys | Cross-carrier access through mis-scoped tokens | | Data model | Applicant records, observations, decision outputs | Database-per-tenant, schema-per-tenant, or row-level controls | Silent data leakage across tenants | | Compute and workflows | Rules engines, queues, background jobs | Tenant-aware orchestration and workload quotas | One tenant influences another tenant's decisions or performance | | Audit and compliance | Logs, evidence, retention policies | Immutable tenant-tagged audit trails | Weak forensic traceability during reviews | | Analytics and exports | BI views, data lake partitions, partner feeds | Segregated datasets and governed extracts | Leakage through reporting rather than core transactions |
The hardest lesson for underwriting vendors is that shared infrastructure is not the same thing as shared context. Carrier A and Carrier B may use the same orchestration engine, but they should not inherit each other's rules, support visibility, or analytics outputs just because the application stack is common.
Choosing the right tenant-isolation model for carrier health data
Most platforms end up choosing among three broad data-isolation patterns.
| Model | How it works | Best fit | Tradeoff profile | |---|---|---|---| | Database per tenant | Each carrier gets its own database instance or cluster | Large carriers, stricter segregation requirements, bespoke retention rules | Strongest separation, highest operational overhead | | Schema per tenant | Shared database engine, separate schemas for each carrier | Mid-market multi-carrier platforms with moderate customization | Balanced operational efficiency and cleaner isolation | | Shared schema with tenant controls | One schema, tenant ID plus strict policy enforcement | High-scale platforms needing faster onboarding and lower infrastructure cost | Efficient, but governance and query discipline must be excellent |
NIST's cloud guidance does not prescribe one exact model, but it makes the accountability point clearly: the customer organization still owns security and privacy outcomes even when the infrastructure is outsourced. For underwriting platforms, that pushes teams to choose isolation patterns based on the sensitivity of carrier workflows, not just cost-per-tenant.
A database-per-tenant model is usually the easiest story to tell a carrier security team. It reduces the blast radius of configuration mistakes and simplifies some retention and backup conversations. But it can become expensive and operationally heavy when a vendor supports many small tenants, each with its own environments, restore policies, and release cadence.
A shared-schema model can scale beautifully, yet it only works when enforcement is systematic. The moment tenant scoping depends on developers remembering one more filter clause, the design is too fragile for health-data workflows.
Why row-level controls matter even in shared models
The industry keeps relearning the same lesson: application-level checks are not enough by themselves. If the query layer does not enforce tenant scope, reporting jobs, support tools, and ad hoc scripts become leakage paths. That is why modern platform teams increasingly push isolation closer to the data layer through policies, tenant-aware indexes, and signed context passed through every request path.
The underwriting implication is straightforward. Shared models can be viable, but only when the database, caches, queues, and analytics layers all understand tenant identity as a first-class attribute.
Industry applications
Carrier-hosted digital underwriting stacks
Large carriers running branded experiences across products or geographies often look multi-tenant even when they think of themselves as single enterprise systems. They may have separate business units, delegated underwriting teams, or regional operating companies that need shared tooling but isolated data boundaries. In these environments, multi-tenancy supports reuse, but governance often pushes the architecture toward stronger partitioning and more explicit policy control.
MGA and distribution platform ecosystems
MGAs and embedded distributors often need a shared operating layer that can support multiple capacity partners. Here, the real challenge is not just data storage. It is preventing one carrier's appetite, referral logic, or screening workflow from bleeding into another carrier's program. Tenant isolation becomes a commercial requirement as much as a security one.
Vendor platforms serving many carrier clients
This is where the architectural tradeoffs are most visible. A vendor needs onboarding speed, common APIs, and efficient release management, but each client expects confidentiality, auditable controls, and tenant-specific operational behavior. Microsoft noted in its 2021 work with HITRUST on a shared responsibility matrix that cloud environments require explicit clarity on which controls are handled by the provider and which remain with the customer. That same shared-responsibility logic shows up in underwriting platforms: infrastructure controls may be standardized, while access models, retention decisions, and workflow approvals often stay carrier-specific.
Current research and evidence
The evidence base for multi-tenant underwriting architecture comes from cloud-security guidance, industry standards, and software architecture research more than clinical literature. Even so, several sources are directly useful.
Wayne Jansen and Timothy Grance at NIST wrote in SP 800-144 that organizations remain accountable for the security and privacy of their cloud-deployed applications and data. That principle matters because carrier platforms sometimes assume a cloud vendor's controls automatically solve tenant-isolation problems. They do not. Accountability still rests with the platform operator and the carrier using it.
NIST SP 800-210 extends the discussion into access control for cloud systems, which is especially relevant for underwriting environments with many internal users, APIs, and service-to-service calls. The practical message is that isolation is not only about storage. It is about making sure access decisions stay consistent across the whole system.
ACORD's standards work offers a second signal. In announcing the ADEPT platform expansion in 2024, ACORD Solutions Group emphasized standards-based digital messaging to reduce manual effort and improve data quality across insurance ecosystems. That is not a tenant-isolation paper, but it does reinforce an important platform point: standardized exchanges make it easier to separate core observations, transaction metadata, and downstream carrier-specific workflows without inventing a new format for every client.
Academic software architecture adds a third perspective. Bezemer and Zaidman argued that multi-tenancy can deliver meaningful scale and maintenance advantages, but only when the architecture is designed deliberately. Underwriting platforms are a good example of that boundary. Shared tenancy can reduce operational cost, but if identity, rules, and audit design lag behind, the maintenance savings disappear into exception handling and client-specific workarounds.
A final lesson comes from healthcare-oriented cloud architecture. AWS engineers describing multi-tenant healthcare search environments emphasized the need for tenant-aware indexing and access controls in shared systems. The lesson carries into underwriting: even when health data is only one component of the workflow, any shared analytical or search layer has to preserve tenant boundaries just as carefully as the transaction store does.
The future of multi-tenant underwriting platform health data isolation
The future probably belongs to platforms that can prove isolation rather than simply promise it. Carrier buyers are asking harder questions about audit evidence, support access, environment design, and downstream analytics boundaries. They want to know whether a platform can show who accessed what, under which tenant context, with which retention rule, and how that context was preserved through APIs, events, and exports.
That should gradually push the market toward a few predictable patterns:
- stronger tenant-aware identity and token design
- more policy enforcement at the data layer
- clearer separation of operational stores and analytics stores
- better evidence packages for carrier security reviews
- standards-based data contracts that reduce custom mappings across tenants
The architectural winner will not necessarily be the platform with the most isolated infrastructure in every case. It will be the one that matches isolation strength to carrier risk, proves its controls, and avoids turning every new tenant into a custom engineering project.
Frequently Asked Questions
What is the biggest risk in a multi-tenant underwriting platform?
The biggest risk is silent cross-tenant exposure, where data, logs, reports, or support tools reveal one carrier's health or applicant information to another. In practice, those failures often happen outside the main transaction flow.
Is database-per-tenant always the safest option?
It is often the simplest isolation model to explain and audit, but not always the best operational choice. Some platforms can safely use shared models if identity, query enforcement, logging, and analytics separation are implemented rigorously.
Does cloud compliance automatically solve carrier data isolation?
No. Cloud certifications and inherited controls help, but the underwriting platform operator still has to design tenant boundaries into identity, storage, workflow, and reporting layers.
Why does standards work matter for multi-tenant underwriting?
Standards reduce custom mappings and make tenant-specific workflows easier to manage. When observations, events, and insurance transactions are modeled consistently, it becomes easier to isolate and govern them across carriers.
For platform teams designing shared underwriting infrastructure, solutions like Circadify's custom builds and API environments are aimed at carrier-grade integration patterns rather than one-off demos. Related reading: FHIR vs Proprietary Formats: How to Model Health Screening Payloads and How to Sandbox and Load Test a Digital Underwriting API Before Launch.